ColdProxy Blog
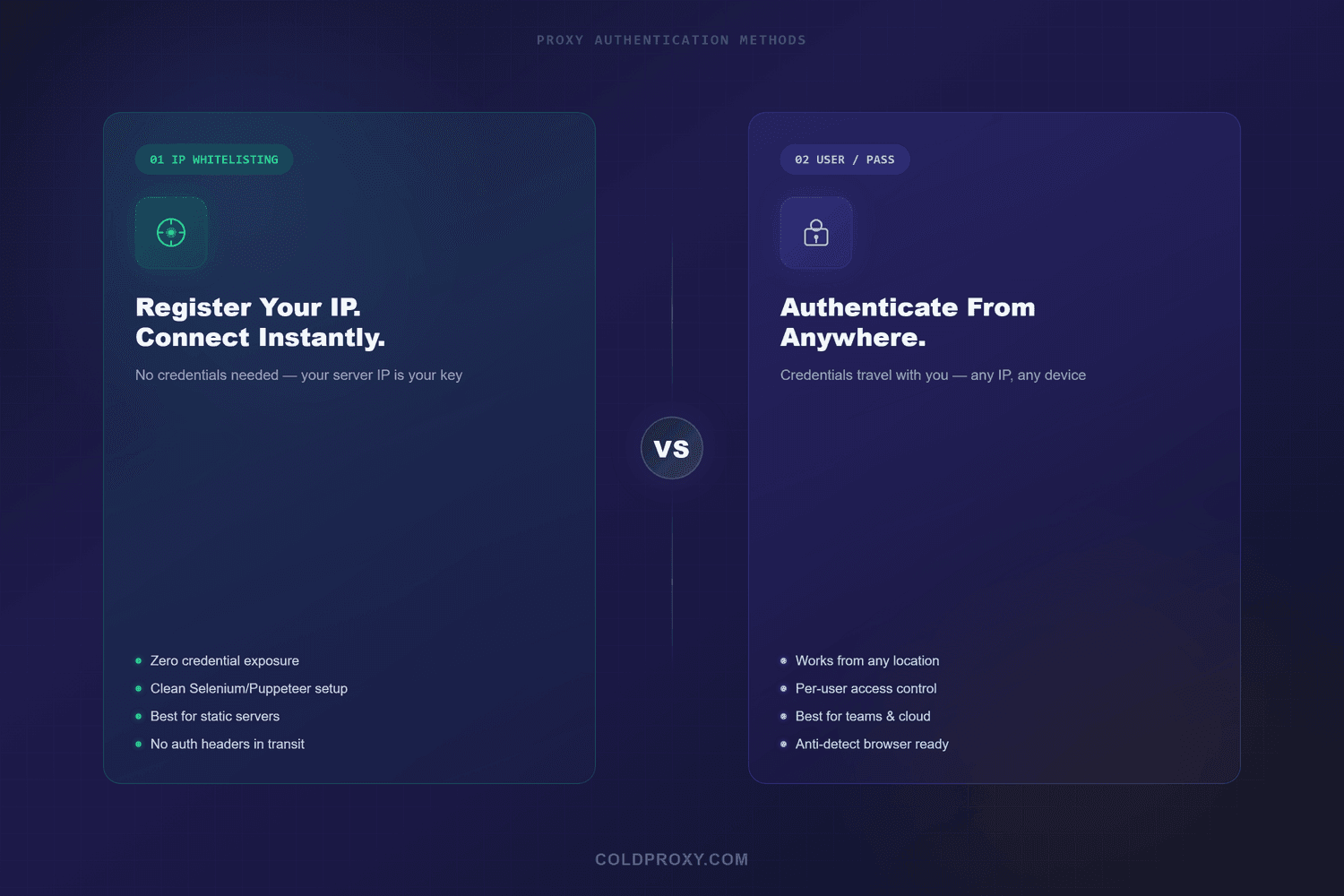
Proxy Authentication Methods: IP Whitelisting vs Username/Password
Key Takeaways
- IP whitelisting works best for fixed-server deployments where your IP address doesn't change — no credentials to manage or expose.
- Username/password authentication is the better choice when you connect from multiple locations, work on a team, or run containers with dynamic IPs.
- For high-security operations, combine both methods: whitelist your server IPs and require credentials, creating defense in depth.
- ColdProxy supports both methods across all four proxy products, with IP whitelist limits scaling from 5 to 40 addresses depending on your plan.
Every proxy connection starts with one question: how does the proxy server know you're allowed to use it? The answer depends on which authentication method you choose — and picking the wrong one can mean leaked credentials, broken automations, or unnecessary setup friction.
The two standard methods are IP whitelisting (the proxy recognizes your server's IP address) and username/password authentication (you send credentials with each request). Both are defined in HTTP standards — specifically RFC 7235 — but they solve different operational problems. This guide breaks down how each method works, where each one fits best, and how to decide for your specific setup.
How Proxy Authentication Actually Works
When your script or browser connects through a proxy, the proxy server needs to verify that the request is authorized. Without authentication, anyone who discovers the proxy address could route traffic through it — burning through your bandwidth, polluting your IP reputation, or racking up charges on your account.
The HTTP specification handles this through a challenge-response flow. When an unauthenticated request hits the proxy, the server returns a 407 (Proxy Authentication Required) status code along with a Proxy-Authenticate header that tells the client which authentication schemes are accepted. The client then retransmits the request with a Proxy-Authorization header containing the appropriate credentials.
That's the textbook version. In practice, most proxy providers simplify this into two approaches: check the client's IP address against an approved list, or check the username and password sent with each request. Some providers support both simultaneously.
IP Whitelisting: How It Works and When to Use It
IP whitelisting (also called IP authorization) is the simpler of the two methods. You register your server's public IP address with your proxy provider. From that point, any connection originating from that IP is automatically authorized — no credentials are transmitted with each request.
Think of it like a building security system that recognizes employee badge IDs. Once your badge is registered, you walk through the door without typing a code every time.
Advantages of IP whitelisting
- Zero credential exposure. There are no passwords to leak in log files, error messages, version control, or Proxy-Authorization headers. This eliminates an entire class of security vulnerabilities.
- Simpler automation scripts. Your code doesn't need to manage credentials, environment variables, or secret stores for proxy access. The connection just works from the registered IP.
- Better compatibility with HTTPS and Selenium. IP authentication avoids the Proxy-Authorization header entirely, which means no 407 challenge-response cycle. This matters for browser automation tools that don't handle proxy auth dialogs cleanly.
- Slightly lower request overhead. Without credential verification on each request, there's a marginal performance gain — relevant at very high request volumes.
Limitations of IP whitelisting
- Dynamic IPs break access. If your ISP assigns a new IP address — which happens regularly with residential internet connections — your proxy access stops until you update the whitelist.
- Limited locations. Most providers restrict how many IPs you can whitelist. If you need proxy access from 10 different servers, you'll need a plan that supports 10 whitelist slots.
- Shared network risks. On a shared hosting environment or office network with a single public IP, anyone on that network could potentially access your proxies.
- Container and serverless challenges. Docker containers, Kubernetes pods, and serverless functions often get dynamic IPs. IP whitelisting isn't practical when your infrastructure doesn't have a stable outbound address.
IP whitelisting setup example
Once your IP is registered with your provider, connecting through the proxy requires no credentials in your code:
import requests
# No credentials needed — your server IP is already whitelisted
proxies = {
"http": "http://gateway.coldproxy.com:7777",
"https": "http://gateway.coldproxy.com:7777"
}
response = requests.get("https://httpbin.org/ip", proxies=proxies)
print(response.json())Compare that simplicity with the credential-based approach below. No environment variables to manage, no risk of credentials appearing in stack traces.
Username/Password Authentication: How It Works and When to Use It
Username/password authentication sends credentials with every proxy request. In HTTP, this uses the Basic Access authentication scheme — your username and password are Base64-encoded (not encrypted) and included in the Proxy-Authorization header.
That encoding detail matters. Base64 is reversible — it's not a security layer. Anyone who intercepts the header can decode it immediately. That's why you should always use HTTPS or SOCKS5 connections when authenticating with credentials, so the proxy URL itself is encrypted in transit.
Advantages of username/password authentication
- Location-independent access. Your credentials work from any IP address — your office, a coffee shop, a cloud instance in a different region, or a newly provisioned container.
- Per-user accountability. In a team, you can issue separate credentials per person or per project. If access needs to be revoked, you disable one set of credentials without affecting everyone else.
- Works with dynamic infrastructure. Kubernetes pods, Docker containers, CI/CD runners, and serverless functions all get dynamic IPs. Credentials work regardless of where the traffic originates.
- Integrates with anti-detect browsers. Tools like Multilogin, GoLogin, and AdsPower expect proxy credentials in a username:password format. IP whitelisting often requires additional workarounds with these tools.
Limitations of username/password authentication
- Credential exposure risk. If proxy URLs with embedded credentials end up in log files, error messages, CI/CD output, or version control, anyone who sees them gets full access. Store credentials in environment variables or a secrets manager — never hardcode them.
- More code complexity. Every script needs to load credentials, handle authentication failures, and potentially retry on 407 responses.
- Browser automation friction. Some automation frameworks don't handle the HTTP 407 challenge-response gracefully, leading to popup dialogs or failed requests that need extra handling code.
Username/password setup example
With credential-based auth, you embed your username and password in the proxy URL or pass them separately:
import requests
import os
# Load credentials from environment variables
proxy_user = os.environ["PROXY_USER"]
proxy_pass = os.environ["PROXY_PASS"]
proxies = {
"http": f"http://{proxy_user}:{proxy_pass}@gateway.coldproxy.com:7777",
"https": f"http://{proxy_user}:{proxy_pass}@gateway.coldproxy.com:7777"
}
response = requests.get("https://httpbin.org/ip", proxies=proxies)
print(response.json())Notice the credentials come from environment variables, not hardcoded strings. The OWASP Authentication Cheat Sheet recommends this as a baseline practice for any credential-bearing application.
Side-by-Side Comparison: IP Whitelisting vs Username/Password
The table below summarizes the practical differences across the criteria that matter most when choosing an authentication method.
| Criteria | IP Whitelisting | Username/Password |
|---|---|---|
| Setup complexity | Register IP once | Store and manage credentials |
| Credential exposure risk | None — no credentials exist | Moderate — credentials can leak in logs or code |
| Location flexibility | Fixed to whitelisted IPs only | Works from any IP address |
| Dynamic infrastructure | Poor — containers and serverless get new IPs | Strong — credentials work anywhere |
| Team access control | Shared — anyone on the whitelisted IP gets access | Granular — per-user or per-project credentials |
| Browser automation | Clean — no auth headers needed | May trigger 407 dialogs in some tools |
| Anti-detect browsers | Requires workarounds | Native support in most tools |
| Revocation speed | Instant — remove IP from list | Instant — disable credentials |
| Best for | Dedicated servers, fixed VPS, browser scraping | Teams, cloud-native, multi-location, anti-detect tools |
Choosing the Right Method for Your Workflow
The right authentication method depends on your infrastructure, team size, and use case — not on which method is theoretically "more secure." Both methods are secure when used correctly and vulnerable when used carelessly.
Use IP whitelisting when
- Your traffic originates from one or a few servers with static IPs (a dedicated VPS, a fixed cloud instance, or an on-premises machine).
- You're running browser automation with Selenium, Puppeteer, or Playwright and want to avoid proxy auth dialogs.
- You want the simplest possible setup for web scraping workflows where credential management adds unnecessary complexity.
- You're a solo operator and don't need per-user access tracking.
Use username/password when
- You connect from multiple locations or devices (office, home, cloud, mobile).
- Your infrastructure uses dynamic IPs — Docker, Kubernetes, CI/CD runners, or serverless functions.
- You work on a team and need separate credentials per person for accountability and access control.
- You use anti-detect browsers (Multilogin, GoLogin, AdsPower) that expect credentials in user:pass format.
Use both methods together when
- You're running production scraping or monitoring at scale and need defense in depth.
- Your compliance requirements mandate multi-factor authentication on outbound connections.
- You handle sensitive data collection where unauthorized proxy access could create legal or financial exposure.
How ColdProxy Handles Authentication
All four ColdProxy proxy plans support both IP whitelisting and username/password authentication. You're not locked into one method — you can switch between them or use both simultaneously depending on what your workflow requires.
Here's what that looks like in practice across the product lineup:
- Premium Residential Geo Target IPv4 (GB Based) — supports HTTPS & SOCKS5 + QUIC protocols with IP whitelist or user/pass auth. Whitelist slots range from 5 to 40 IPs depending on your plan tier.
- Premium Residential Geo Target IPv4 (Unmetered) — same dual auth support with HTTP/HTTPS/SOCKS5 protocol flexibility. Whitelist limits scale from 5 to 40 IPs.
- Residential IPv6 — IP whitelisting or user/pass authentication with the same tiered whitelist limits.
- Datacenter IPv6 — full dual-auth support for high-speed use cases where both security and performance matter.
The tiered whitelist limit is a detail worth noting: entry-level plans support 5 whitelisted IPs, which is plenty for most solo operators or small teams. Higher-tier plans scale up to 40 whitelisted IPs, which is enough to cover multi-server deployments, distributed crawling setups, or teams with dedicated scraping infrastructure across multiple locations.
Security Best Practices for Proxy Authentication
Regardless of which method you choose, proxy authentication is only as strong as your operational practices. These recommendations apply broadly, and you can find more detailed guidance in our proxy security best practices guide.
For IP whitelisting
- Audit your whitelist regularly. Remove IPs for servers you've decommissioned. Stale entries are attack surface.
- Confirm your IP is actually static. Check with your ISP or cloud provider. Many residential connections and some cloud NAT gateways rotate IPs without warning.
- Don't whitelist shared IPs. On shared hosting or office NAT, other users on the same public IP could access your proxy.
- Monitor for unauthorized usage. Even with a whitelisted IP, track your bandwidth consumption to catch unexpected spikes that could indicate abuse from within the same network.
For username/password authentication
- Never hardcode credentials. Use environment variables, .env files (excluded from version control), or a secrets manager like AWS Secrets Manager, HashiCorp Vault, or Doppler.
- Rotate credentials periodically. Change passwords on a regular schedule — quarterly at minimum for production systems. Rotate immediately if you suspect exposure.
- Use separate credentials per project or team member. If one set is compromised, you can revoke it without disrupting everything else.
- Always connect over HTTPS or SOCKS5. Basic auth is Base64-encoded, not encrypted. Without transport-layer encryption, credentials are readable by anyone who can intercept the traffic.
How We Evaluated These Methods
This comparison is based on three sources: the HTTP authentication standards (RFC 7235 and RFC 7617), current proxy provider documentation across multiple vendors, and practical deployment experience with both methods across scraping, monitoring, and multi-account management workflows.
We tested both authentication methods against common infrastructure setups: dedicated VPS with static IP, cloud instances with elastic IPs, Docker containers with bridge networking, and local development machines behind residential ISPs. The comparison table reflects real behavioral differences observed across these environments, not theoretical specifications alone.
ColdProxy-specific details (whitelist limits, protocol support, product names) were verified against the live product pages and WHMCS pricing data on the day this article was published.
Limitations and Edge Cases
A few scenarios don't fit neatly into the comparison above:
- IPv6-only environments may have different whitelisting behavior depending on whether the provider matches /128 (single address) or /64 (subnet) ranges. Check your provider's documentation.
- CGNAT (Carrier-Grade NAT) can make IP whitelisting unreliable even on connections that appear static, because multiple customers share the same public IP. This is increasingly common with some mobile and fixed-wireless ISPs.
- Some corporate firewalls strip or rewrite Proxy-Authorization headers, breaking credential-based auth. If you're behind an enterprise firewall, test the connection before deploying at scale.
- Token-based authentication (API keys, JWT tokens) is emerging as a third option with some providers, but it's not yet standard across the industry. The two methods covered here remain the dominant approaches in 2026.
Frequently Asked Questions
Is IP whitelisting more secure than username/password authentication?
IP whitelisting eliminates credential exposure risk entirely, which makes it stronger against phishing, log leaks, and accidental commits. But it introduces a different risk: anyone who routes traffic through your whitelisted IP gets automatic access. Neither method is universally more secure — the right choice depends on your network architecture and threat model.
Can I use both authentication methods at the same time?
Yes. Combining IP whitelisting with username/password creates defense in depth. An attacker would need both access to your whitelisted IP and valid credentials. This is the recommended approach for production systems handling sensitive data or high-value operations.
What happens if my IP address changes while using IP whitelisting?
Your proxy access stops immediately. You'll need to log into your provider's dashboard and update the whitelist with your new IP. For connections where your IP may change unexpectedly — residential ISPs, mobile networks, or cloud instances without elastic IPs — username/password authentication is the more reliable choice.
Which method works better with anti-detect browsers?
Username/password authentication works natively with most anti-detect browsers (Multilogin, GoLogin, AdsPower). These tools have dedicated fields for proxy credentials and expect the user:pass format. While IP whitelisting can work with some anti-detect setups, it typically requires additional configuration and doesn't offer per-profile isolation.
How many IPs can I whitelist with ColdProxy?
ColdProxy's whitelist limits scale with your plan: entry-level plans support 5 whitelisted IPs, mid-tier plans go up to 10-15, and higher-tier plans allow 20 to 40 whitelisted addresses. Check the specific limits on the pricing page for each product.
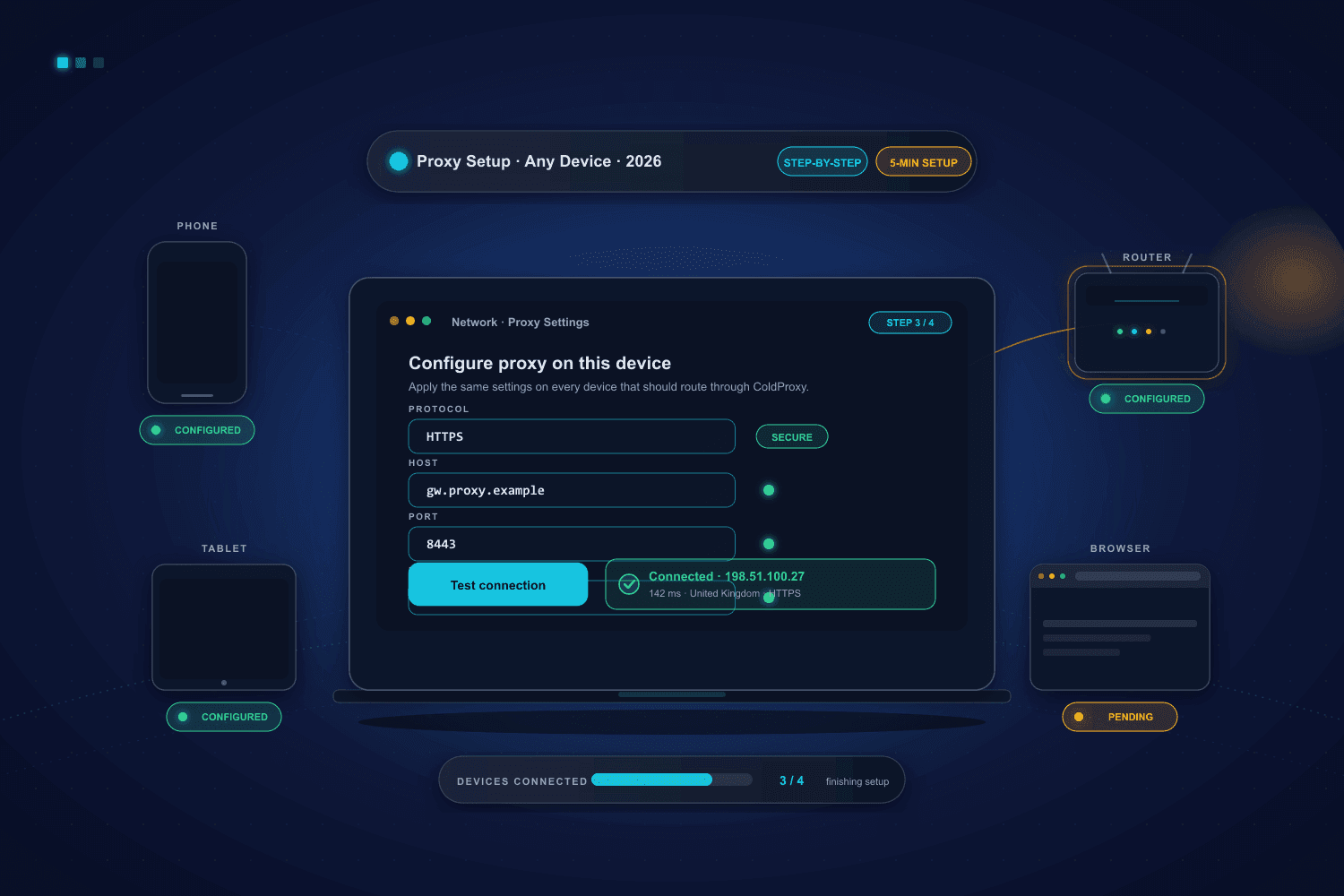
What's Next: Setting Up Your Proxy Connection
Choosing your authentication method is the first decision in getting your proxy workflow running. Once you've decided, the next step is connecting your tools — whether that's a Python script, a browser automation framework, or an anti-detect browser. Our proxy setup guide walks through the full connection process across Windows, Mac, Android, iOS, and common automation tools.
As proxy infrastructure continues evolving — with token-based auth, mutual TLS, and API-first access models gaining ground — the fundamentals covered here remain the foundation. Understanding how IP whitelisting and credential-based authentication work, where each one fits, and how to secure both will serve you well regardless of what the next generation of proxy protocols looks like.